Technical Architecture of Secure Online Banking Systems
Explore the technical architecture of secure online banking systems, including layered security, encryption, authentication, APIs, and fraud detection that protect digital transactions.
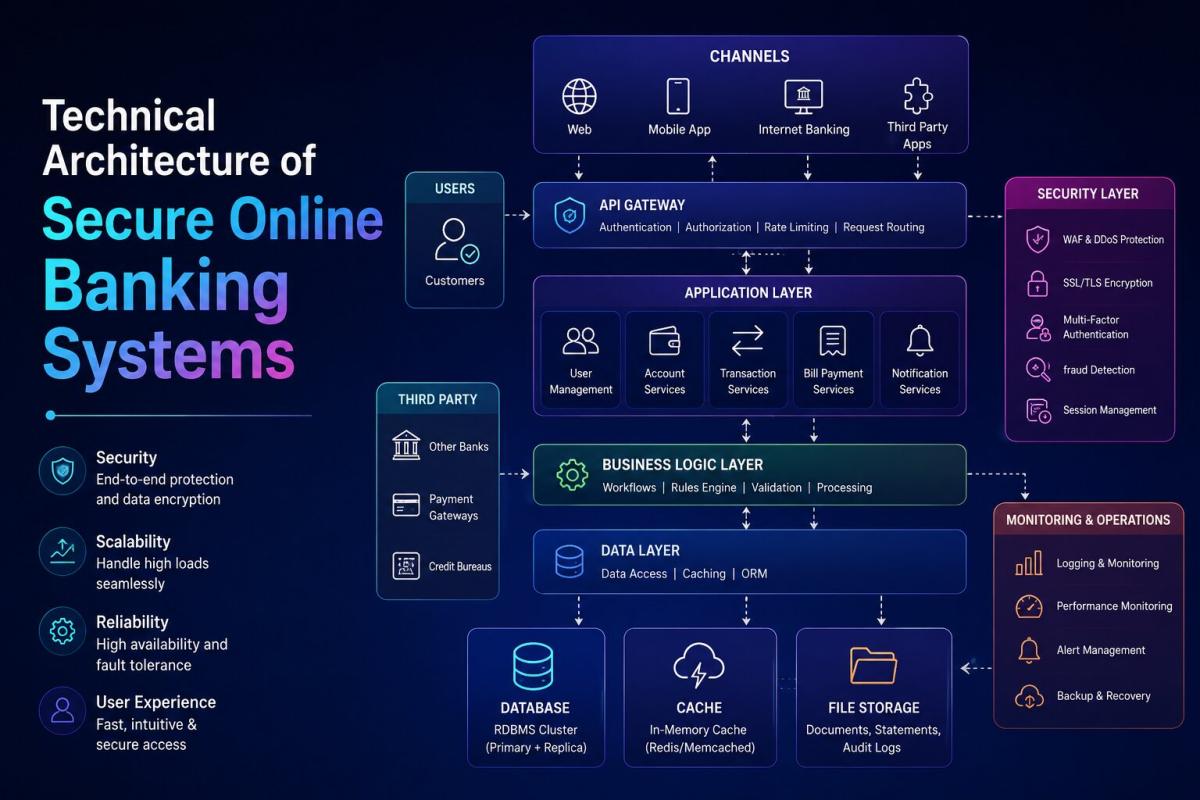
Table of Contents
- Understanding the Foundation of Secure Digital Banking
- Core Layers of Secure Banking Architecture
- Authentication and Identity Management
- Encryption and Data Protection Mechanisms
- Transaction Processing Architecture
- Fraud Detection and Monitoring Systems
- Secure API and Integration Layer
- Secure Banking Architecture Components Comparison
- Cloud Infrastructure and Banking Security
- Regulatory Compliance and Security Standards
- Best Practices for Secure Banking Architecture
- Frequently Asked Questions
- Conclusion
Understanding the Foundation of Secure Digital Banking
Secure online banking systems are built on a deeply layered architecture where every component is designed with protection in mind. These systems go beyond simple transactions and focus on preserving trust, accuracy, and resilience. Frameworks like the National Institute of Standards and Technology Cybersecurity Framework define how institutions should identify risks, protect systems, detect threats, respond effectively, and recover quickly. This structured approach forms the backbone of modern banking security.
Modern banking platforms are engineered to handle millions of secure transactions simultaneously while ensuring that sensitive data remains protected. This is achieved through encryption, layered validation, and continuous monitoring systems that operate silently in the background.
Core Layers of Secure Banking Architecture
Presentation Layer and Secure User Interfaces
The presentation layer is where users interact with the banking system through mobile apps or web platforms. Security at this level focuses on safeguarding login credentials, preventing session hijacking, and ensuring secure communication.
Protocols like Transport Layer Security ensure encrypted data transmission between users and servers. Companies such as Cloudflare emphasize the importance of SSL and TLS in preventing data interception and man in the middle attacks.
Application Layer and Business Logic Security
The application layer processes user requests and executes business rules. It ensures that every transaction follows strict validation checks before being approved.
Modern systems use microservices architecture, a concept widely explained by Martin Fowler, where each function operates independently. This reduces the risk of system wide failure and improves security isolation.
Data Layer and Storage Protection
The data layer is where all sensitive financial information is stored. This includes account details, transaction records, and personal data.
Encryption standards such as AES are recommended by the National Institute of Standards and Technology to ensure that even if data is accessed without authorization, it remains unreadable. Advanced monitoring systems track every database interaction to detect unusual access patterns.
Network Layer and Infrastructure Security
The network layer connects all system components while enforcing strict access controls. Firewalls, intrusion detection systems, and segmented networks ensure that threats are contained before they reach critical systems.
Security models promoted by Cisco highlight the importance of layered network defenses and controlled access zones.
Authentication and Identity Management
Authentication systems verify user identity before granting access. This is one of the most critical components of secure banking architecture.
Multi factor authentication combines passwords, one time passwords, and biometric verification. Security practices outlined by the OWASP recommend using multiple authentication layers to reduce the risk of unauthorized access.
Identity management systems further ensure that users can only access what they are authorized to view or perform.
Encryption and Data Protection Mechanisms
Encryption protects data at every stage, whether it is being transmitted or stored. Hardware security modules are often used to generate and manage encryption keys securely.
Insights from IBM highlight that strong encryption combined with proper key management significantly reduces the chances of data breaches.
Tokenization is also widely used, replacing sensitive data with temporary tokens during transactions.
Transaction Processing Architecture
Transaction processing systems handle validation, execution, and recording of financial operations in real time.
These systems include transaction gateways, validation engines, and core banking platforms. Infrastructure best practices from Amazon Web Services emphasize redundancy and failover systems to maintain uninterrupted service.
Fraud Detection and Monitoring Systems
Fraud detection systems use machine learning and behavioral analysis to identify suspicious activities.
These systems monitor patterns such as unusual transaction sizes or unexpected locations. Cybersecurity insights from Kaspersky show that combining analytics with real time monitoring significantly improves fraud detection accuracy.
Secure API and Integration Layer
APIs enable communication between banking systems and external services. Security at this level is critical to prevent unauthorized data access.
Frameworks like the Open Banking Initiative ensure secure and regulated data sharing between institutions.
API gateways enforce authentication, encryption, and traffic monitoring to maintain system integrity.
Secure Banking Architecture Components Comparison
|
Component |
Primary Function |
Security Measures |
Risk Mitigation |
|
Presentation Layer |
User interaction |
HTTPS encryption, input validation |
Prevents data interception |
|
Application Layer |
Business logic |
Access control, session handling |
Reduces unauthorized actions |
|
Data Layer |
Data storage |
Encryption, monitoring |
Protects sensitive data |
|
Network Layer |
Communication |
Firewalls, segmentation |
Blocks external threats |
|
Authentication System |
Identity verification |
MFA, biometrics |
Prevents account takeover |
|
Fraud Detection |
Risk monitoring |
AI analytics |
Detects anomalies |
Cloud Infrastructure and Banking Security
Cloud computing has transformed banking systems by enabling scalability and advanced protection mechanisms.
Cloud providers such as Google Cloud offer built in encryption, monitoring, and identity management tools. The shared responsibility model ensures that infrastructure is secured while banks focus on application level protection.
Hybrid models allow institutions to maintain compliance while leveraging cloud benefits.
Regulatory Compliance and Security Standards
Banking systems must comply with strict regulations to ensure data protection and operational integrity.
Standards from the PCI Security Standards Council define how payment data should be handled securely. Compliance ensures regular audits and updates to address evolving threats.
Best Practices for Secure Banking Architecture
Strong banking systems rely on continuous improvement and proactive security measures.
Key practices include implementing zero trust models, regular penetration testing, continuous monitoring, strong encryption policies, and employee awareness programs.
These practices ensure that systems remain resilient against modern cyber threats.
Frequently Asked Questions
What makes online banking systems secure
Secure systems use multiple layers including encryption, authentication, network protection, and monitoring to safeguard data and transactions.
How does multi factor authentication help
It adds extra layers of verification, making unauthorized access significantly more difficult.
Are cloud based banking systems safe
Yes, when implemented with proper security controls, encryption, and compliance frameworks.
How do banks detect fraud
Banks use machine learning and behavioral analysis to identify unusual patterns in real time.
Why is encryption important in banking
Encryption ensures that sensitive data remains unreadable even if intercepted or accessed without authorization.
Conclusion
The technical architecture of secure online banking systems is built on precision, layered security, and continuous monitoring. Each component plays a vital role in protecting financial data and ensuring seamless transactions.
As digital banking evolves, new technologies continue to strengthen these systems. Institutions that adopt strong architectural practices and stay aligned with global standards are better equipped to provide secure and reliable services.
Understanding this architecture not only highlights the complexity behind everyday transactions but also reinforces confidence in modern banking systems.
Related Blogs
Published on May 06, 2026
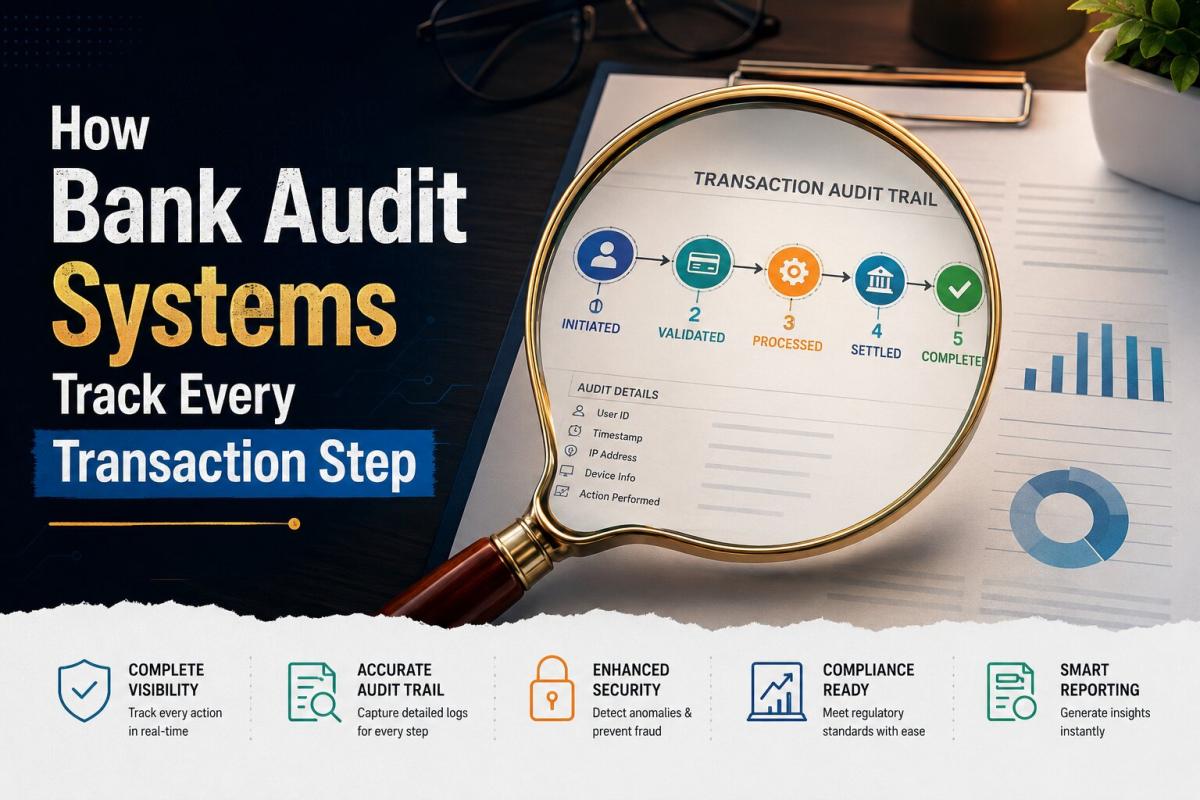
How Bank Audit Systems Track Every Transaction Step
Discover how bank audit systems track every transaction step using audit trails, real-time logging, and AI monitoring to ensure transparency, fraud detection, and regulatory compliance.
Priya Nair
Senior Compliance Editor at IFSC.co
Published on Apr 28, 2026
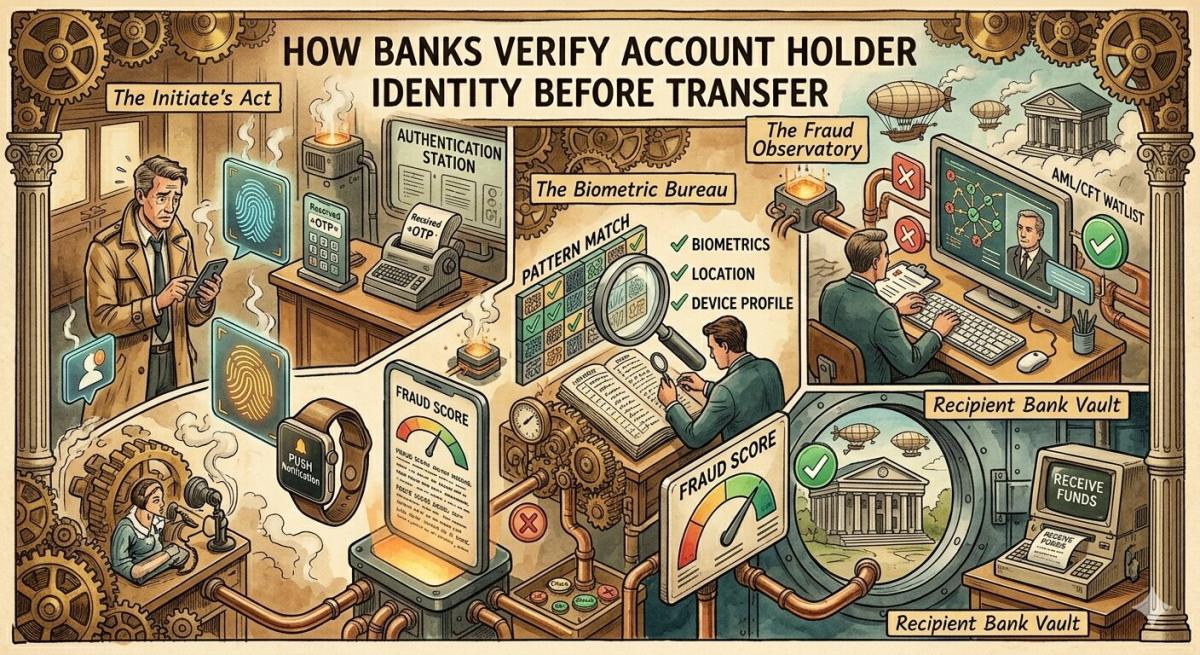
How Banks Verify Account Holder Identity Before Transfer
Learn how banks verify account holder identity before transfers using KYC, OTP, biometrics, and real-time fraud detection to ensure secure and compliant digital transactions.
Priya Nair
Senior Compliance Editor at IFSC.co

Published on Apr 28, 2026
What Causes Silent Bank Transaction Failures Without Alert
Discover the key causes of silent bank transaction failures, including network timeouts, API issues, system delays, and how banks resolve these hidden payment errors.
Priya Nair
Senior Compliance Editor at IFSC.co

Published on Apr 28, 2026
Real Time Bank Transaction Authentication Process Explained
Understand how real-time bank transaction authentication works using OTP, biometrics, encryption, and AI-driven fraud detection to secure digital payments instantly.
Priya Nair
Senior Compliance Editor at IFSC.co

Published on Apr 09, 2026
Fraud Prevention: Security Checks Before Bank Transfer Approval
Learn how banks use KYC verification, AI-powered fraud detection, transaction monitoring, MFA, AML compliance, and human oversight to secure bank transfers and prevent fraud in 2026.
Priya Nair
Senior Compliance Editor at IFSC.co
calculate Financial Calculators
EMI Calculator
FD Calculator
GST Calculator
Lumpsum Calculator
Mutual Fund Returns Calculator
PPF Calculator
RD Calculator
SIP Calculator
SWP Calculator
article Latest Blog Posts
ELSS vs PPF vs NPS: Which Tax-Saving Investment Gives the Best Returns?
Compare ELSS vs PPF vs NPS to find the best tax-saving investment. Understand returns, lock-in periods, and features to choose what suits your goals.
SIP & Investing • 11 MINS READ
How to Start SIP with ₹500 Per Month: Beginner's Guide to Mutual Funds
Learn how to start a SIP with ₹500 per month in mutual funds. Simple beginner’s guide to investing, building wealth, and growing money with small steps.
SIP & Investing • 13 MINS READ
Senior Citizen FD Rates 2026: Which Banks Offer the Highest Interest?
Compare senior citizen FD rates in 2026 and find which banks offer the highest interest. Learn about returns, tenures, and tips to choose the best FD.
FD, PPF & Savings • 12 MINS READ
Sukanya Samriddhi Yojana (SSY): Interest Rate, Rules & Calculator Guide 2026
Learn about Sukanya Samriddhi Yojana (SSY) including eligibility criteria, required documentation, step by step application process, tax benefits explanation and comparison b/w SSY, PPF and FD
FD, PPF & Savings • 11 MINS READ
2 reasons why online banking is important in today’s COVID-19 situation
Discover why online banking became essential during COVID-19. Learn how digital banking ensured safety, convenience, and uninterrupted financial services.
Digital Banking • 4 MINS READ