Fraud Prevention: Security Checks Before Bank Transfer Approval
Learn how banks use KYC verification, AI-powered fraud detection, transaction monitoring, MFA, AML compliance, and human oversight to secure bank transfers and prevent fraud in 2026.

Table of Contents
- Verifying Identity and Onboarding
- Behavioral Analytics and Transaction Monitoring
- AI and Machine Learning in Fraud Detection
- Regulatory Compliance and Sanctions Screening
- Multi-Factor Authentication (MFA) and Authorization
- Human Oversight and Escalation Procedures
- Key Takeaways
- Frequently Asked Questions
- Conclusion
Just last year, a friend of mine almost lost a significant sum to a sophisticated phishing scam. The email looked legitimate, the website mirrored his bank’s, and he was moments away from authorizing a hefty transfer to what he thought was a new investment account. It was a stark reminder that while fraudsters are constantly innovating, so too are the financial institutions dedicated to protecting our money. The intricate web of security checks applied before approving a bank transfer isn’t just about compliance; it’s a dynamic, multi-layered defense system designed to safeguard your assets, maintain trust, and prevent illicit activities from ever reaching their target. Understanding these unseen guardians offers a profound appreciation for the security infrastructure underpinning modern finance.
Verifying Identity and Onboarding
Before any transfer can even be considered, banks establish a robust foundation of identity verification during account opening. This process, known as Know Your Customer (KYC), involves meticulously collecting and validating personal information, often requiring government-issued identification, proof of address, and sometimes even biometric data. The goal is to ensure that the individual or entity initiating the transfer is genuinely who they claim to be, preventing fraudsters from establishing accounts under false pretenses. This initial rigorous vetting forms the bedrock of trust, making it significantly harder for criminals to infiltrate the system from the outset.
These foundational checks are continuously updated and cross-referenced with various databases to ensure ongoing legitimacy. For instance, a bank might routinely check for changes in a customer’s registered details or look for inconsistencies that could signal account compromise. This proactive approach helps financial institutions stay ahead of evolving fraud tactics, particularly those involving identity theft. Without this stringent initial and ongoing verification, the subsequent security layers would be far less effective, highlighting the critical importance of a thorough and vigilant onboarding process in the broader scheme of financial security.
Behavioral Analytics and Transaction Monitoring
Once an account is established, every transaction, including bank transfers, undergoes real-time scrutiny through sophisticated behavioral analytics. These systems learn your typical spending habits, transfer patterns, common beneficiaries, and even the devices and locations you usually access your banking from. If a transfer request deviates significantly from this established norm – perhaps a large sum to a new recipient in an unusual country, initiated from an unfamiliar IP address – it immediately raises a red flag. This proactive monitoring is a crucial line of defense against unauthorized access and fraudulent transactions.
The algorithms powering these analytics are incredibly advanced, capable of sifting through vast amounts of data in milliseconds to identify anomalies that human eyes might miss. They consider not just the amount and recipient but also the time of day, frequency of transfers, and even the keystroke dynamics of the user. This intelligent monitoring system doesn’t just block suspicious activity; it learns from every interaction, constantly refining its ability to distinguish legitimate but unusual transactions from genuine fraud attempts. It’s a testament to how data science has become indispensable in protecting our financial well-being.
AI and Machine Learning in Fraud Detection
The cutting edge of behavioral analytics lies in the application of Artificial Intelligence (AI) and Machine Learning (ML). These technologies enable systems to not only identify known fraud patterns but also to detect entirely new, emerging threats by recognizing subtle correlations and deviations that are too complex for traditional rule-based systems. AI models are continuously trained on massive datasets of both legitimate and fraudulent transactions, allowing them to adapt quickly to new attack vectors and sophisticated scams. This adaptive learning capability is vital in the ever-evolving landscape of cybercrime.
By leveraging AI, banks can significantly reduce false positives, meaning fewer legitimate transactions are unnecessarily delayed or blocked, improving the customer experience without compromising security. Furthermore, ML algorithms can process and analyze data from various sources simultaneously, including social media, dark web forums, and global threat intelligence feeds, providing a holistic view of potential risks. This intelligent automation empowers banks to make faster, more accurate decisions, ensuring that by 2026, financial security will be more robust and responsive than ever before, thanks to these technological advancements.
Regulatory Compliance and Sanctions Screening
Beyond protecting individual customers, banks have a profound responsibility to uphold global financial integrity. This involves stringent adherence to regulatory compliance frameworks such as Anti-Money Laundering (AML) and Counter-Terrorist Financing (CTF) laws. Before a bank transfer is approved, it undergoes rigorous screening against international sanctions lists, like those maintained by the Office of Foreign Assets Control (OFAC). This ensures that funds are not being sent to individuals, entities, or countries associated with terrorism, drug trafficking, or other illicit activities, thereby preventing the financial system from being exploited by criminal networks.
The process of sanctions screening is complex and dynamic, requiring constant updates to reflect new designations and changes in geopolitical landscapes. Banks employ specialized software that cross-references all parties involved in a transaction – sender, receiver, and intermediary banks – against these comprehensive lists. Any potential match triggers an immediate hold and further investigation by compliance officers. This meticulous process isn’t just about avoiding penalties; it’s a critical ethical imperative to choke off funding for global criminal enterprises, making our world safer by preventing the financing of nefarious activities. You can learn more about these global efforts on the FinCEN website.
Multi-Factor Authentication (MFA) and Authorization
Even if an account has been compromised through phishing or malware, Multi-Factor Authentication (MFA) serves as a powerful barrier against unauthorized transfers. MFA requires users to provide two or more verification factors from different categories before access is granted or a transaction is approved. This typically involves something you know (like a password), something you have (like a phone receiving a one-time passcode or a hardware token), and sometimes something you are (like a fingerprint or facial scan). It dramatically reduces the risk of an attacker gaining full control, even with stolen credentials.
For bank transfers specifically, MFA often manifests as a final authorization step. After initiating a transfer, you might be prompted to enter a code sent to your registered mobile device, approve the transaction via your banking app, or even provide a biometric scan. This critical extra layer ensures that the person attempting to move funds is indeed the legitimate account holder, acting with explicit consent. It’s a vital safeguard, transforming a single point of failure (your password) into a layered defense system that is significantly harder for criminals to breach, offering peace of mind in our increasingly digital financial lives. For a deeper dive into MFA, check out resources from cybersecurity experts like CISA.
Human Oversight and Escalation Procedures
While technology forms the backbone of modern security, the human element remains irreplaceable. Automated systems are excellent at flagging anomalies, but complex or ambiguous cases often require the nuanced judgment of experienced fraud analysts. When a transaction triggers multiple red flags or falls into a grey area, it’s escalated for manual review. These analysts examine the full context of the transaction, cross-reference historical data, and often directly contact the customer to verify the legitimacy of the transfer. This human intervention ensures that genuinely suspicious activities are caught, while legitimate but unusual transfers are not unfairly blocked.
The training and expertise of these fraud teams are paramount. They are continuously updated on the latest scam tactics, social engineering techniques, and global fraud trends. Their role involves a delicate balance: protecting the bank and its customers without unduly inconveniencing legitimate transactions. In instances of confirmed fraud, they initiate immediate action to freeze funds, alert law enforcement, and guide customers through the recovery process. This blend of cutting-edge AI and seasoned human expertise is what truly fortifies the financial system against the relentless ingenuity of fraudsters, creating a robust defense for your funds in 2026 and beyond.
Key Takeaways
- Layered Security is Paramount: Bank transfer security isn’t a single switch but a complex, multi-layered defense system encompassing identity verification, behavioral analysis, regulatory compliance, and strong authentication.
- AI and Human Expertise Combine: Automated systems using AI and Machine Learning efficiently identify anomalies, while skilled human analysts provide crucial oversight and nuanced judgment for complex or ambiguous cases.
- Regulatory Compliance Protects Everyone: Strict adherence to AML, CTF, and sanctions screening regulations prevents financial systems from being exploited by criminal organizations, safeguarding global financial integrity.
- Your Role in Security is Vital: Employing strong, unique passwords, enabling MFA, and remaining vigilant against phishing attempts are critical steps you can take to bolster the security of your bank transfers.
Frequently Asked Questions
What happens if my bank transfer is flagged for security review?
If your bank transfer is flagged, it typically means the bank’s automated systems have detected an unusual pattern or a potential risk. The transfer will likely be temporarily put on hold, and you may be contacted by your bank via your registered phone number or email to verify the transaction’s legitimacy. Respond promptly to these requests to avoid unnecessary delays.
Can I speed up the security checks for urgent bank transfers?
While you cannot bypass security checks, which are in place for your protection, ensuring your contact information with the bank is always up-to-date can help. If a transfer is flagged, the bank can reach you quickly for verification, minimizing delays. For very large or unusual transfers, informing your bank beforehand might also help streamline the process.
Are security checks different for international bank transfers compared to domestic ones?
Yes, international bank transfers generally involve additional layers of security and compliance checks due to varying international regulations, currency conversions, and the involvement of multiple financial institutions across different jurisdictions. These often include more rigorous sanctions screening and AML checks to comply with global standards.
What is the biggest threat to bank transfer security in 2026?
In 2026, the biggest threat to bank transfer security is likely to be sophisticated social engineering tactics, often amplified by AI, leading to authorized push payment (APP) fraud. Fraudsters manipulate individuals into willingly authorizing payments to accounts they control, making it challenging for banks to differentiate legitimate from fraudulent transactions, despite robust technical controls.
Conclusion
The journey of a bank transfer from initiation to approval is far more intricate than most realize, underscored by a relentless dedication to security. From the initial KYC checks to advanced AI-driven behavioral analytics, multi-factor authentication, and the indispensable human oversight, every layer is designed to protect your funds and uphold the integrity of the financial system. As technology evolves, so too do the defenses, ensuring that by 2026, banks remain vigilant guardians of your financial well-being. Your awareness and proactive security habits, combined with these robust systems, form an unbeatable partnership in the fight against financial crime.
Related Blogs
Published on May 06, 2026
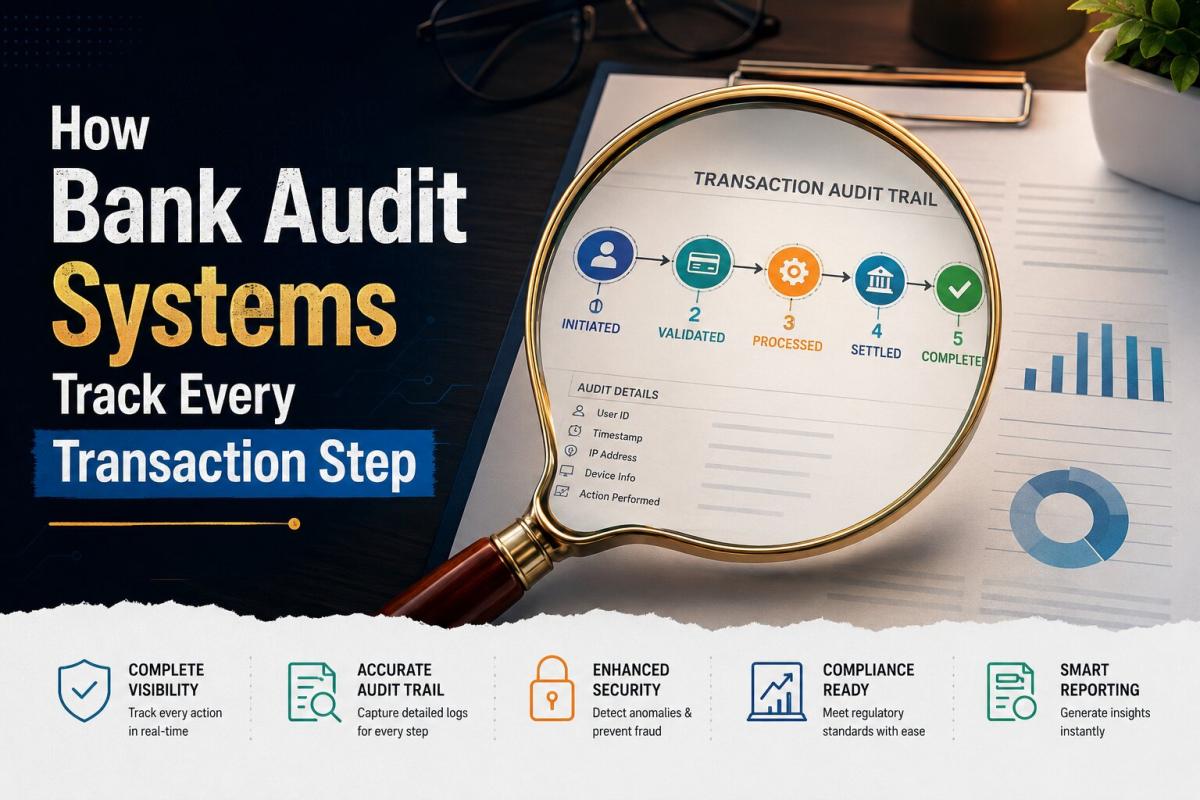
How Bank Audit Systems Track Every Transaction Step
Discover how bank audit systems track every transaction step using audit trails, real-time logging, and AI monitoring to ensure transparency, fraud detection, and regulatory compliance.
Priya Nair
Senior Compliance Editor at IFSC.co
Published on May 06, 2026
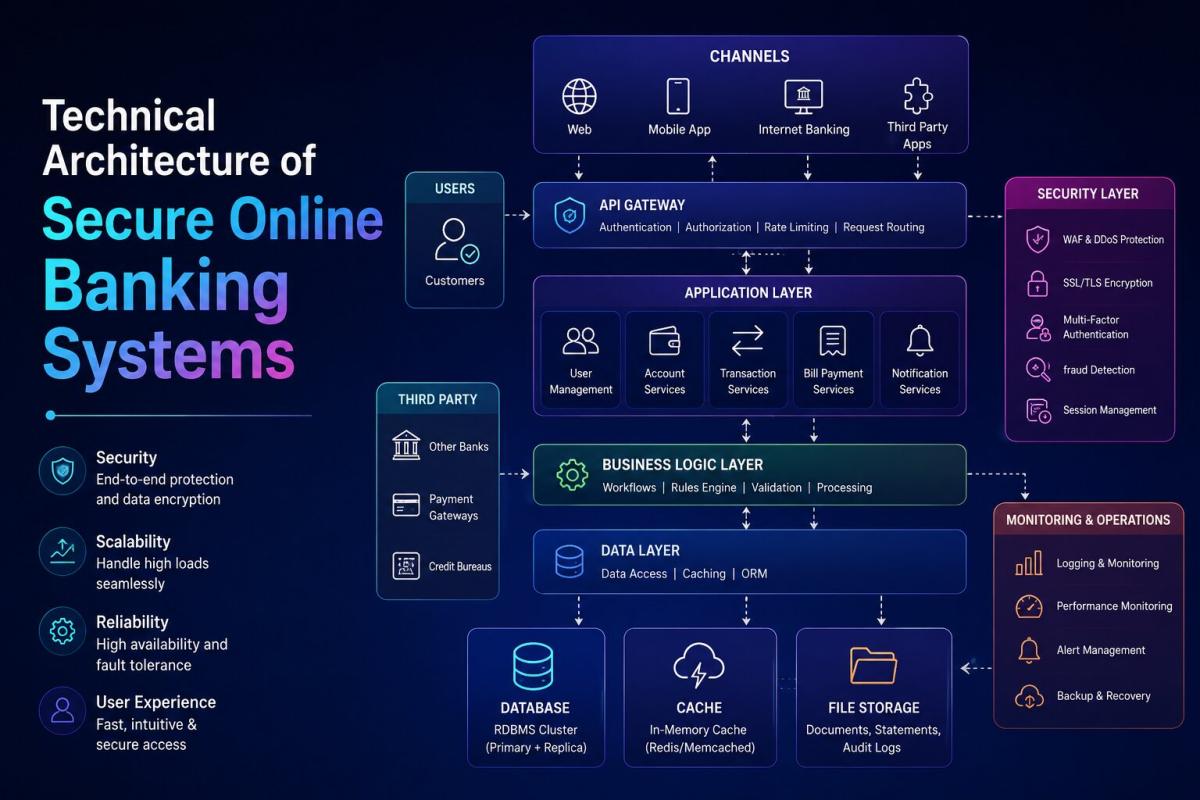
Technical Architecture of Secure Online Banking Systems
Explore the technical architecture of secure online banking systems, including layered security, encryption, authentication, APIs, and fraud detection that protect digital transactions.
Priya Nair
Senior Compliance Editor at IFSC.co
Published on Apr 28, 2026
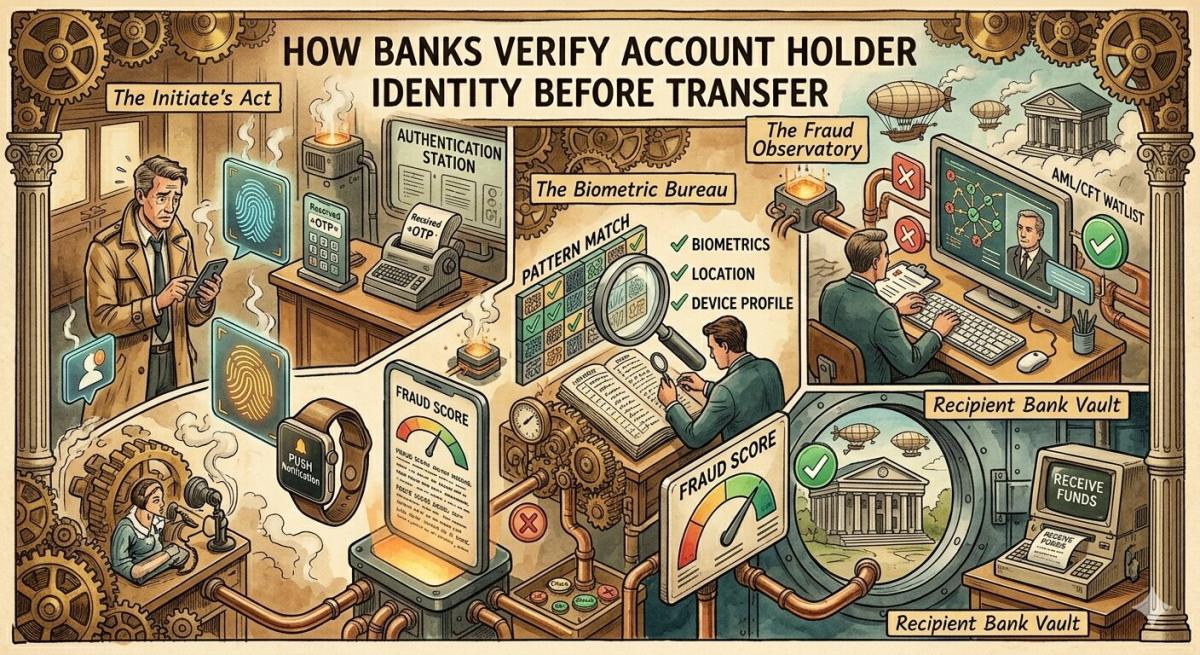
How Banks Verify Account Holder Identity Before Transfer
Learn how banks verify account holder identity before transfers using KYC, OTP, biometrics, and real-time fraud detection to ensure secure and compliant digital transactions.
Priya Nair
Senior Compliance Editor at IFSC.co

Published on Apr 28, 2026
What Causes Silent Bank Transaction Failures Without Alert
Discover the key causes of silent bank transaction failures, including network timeouts, API issues, system delays, and how banks resolve these hidden payment errors.
Priya Nair
Senior Compliance Editor at IFSC.co

Published on Apr 28, 2026
Real Time Bank Transaction Authentication Process Explained
Understand how real-time bank transaction authentication works using OTP, biometrics, encryption, and AI-driven fraud detection to secure digital payments instantly.
Priya Nair
Senior Compliance Editor at IFSC.co
calculate Financial Calculators
EMI Calculator
FD Calculator
GST Calculator
Lumpsum Calculator
Mutual Fund Returns Calculator
PPF Calculator
RD Calculator
SIP Calculator
SWP Calculator
article Latest Blog Posts
ELSS vs PPF vs NPS: Which Tax-Saving Investment Gives the Best Returns?
Compare ELSS vs PPF vs NPS to find the best tax-saving investment. Understand returns, lock-in periods, and features to choose what suits your goals.
SIP & Investing • 11 MINS READ
How to Start SIP with ₹500 Per Month: Beginner's Guide to Mutual Funds
Learn how to start a SIP with ₹500 per month in mutual funds. Simple beginner’s guide to investing, building wealth, and growing money with small steps.
SIP & Investing • 13 MINS READ
Senior Citizen FD Rates 2026: Which Banks Offer the Highest Interest?
Compare senior citizen FD rates in 2026 and find which banks offer the highest interest. Learn about returns, tenures, and tips to choose the best FD.
FD, PPF & Savings • 12 MINS READ
Sukanya Samriddhi Yojana (SSY): Interest Rate, Rules & Calculator Guide 2026
Learn about Sukanya Samriddhi Yojana (SSY) including eligibility criteria, required documentation, step by step application process, tax benefits explanation and comparison b/w SSY, PPF and FD
FD, PPF & Savings • 11 MINS READ
2 reasons why online banking is important in today’s COVID-19 situation
Discover why online banking became essential during COVID-19. Learn how digital banking ensured safety, convenience, and uninterrupted financial services.
Digital Banking • 4 MINS READ