Encryption Explained: How Online Banking Stays Secure
Learn how encryption protects online banking through TLS, SSL, digital certificates, symmetric and asymmetric encryption, hashing, and multi-factor authentication in 2026.

Table of Contents
Remember those early days of the internet, when the mere thought of entering credit card details online sent shivers down your spine? It felt like shouting your secrets into a vast, unmonitored void. Fast forward to today, and we confidently manage our entire financial lives through a smartphone app or web browser, often without a second thought. This monumental shift in trust isn’t magic; it’s the quiet, relentless power of encryption at work. Understanding how encryption works in online banking systems is not just for tech enthusiasts; it’s for anyone who wants to truly appreciate the invisible fortress safeguarding their money.
The Foundation: SSL/TLS Handshake
Every time you connect to your bank’s website, an intricate dance begins before any data even leaves your device. This dance is known as the Transport Layer Security (TLS) handshake, formerly and often still colloquially referred to as Secure Sockets Layer (SSL). It’s the critical first step in establishing a secure, encrypted channel between your browser and the bank’s server. Think of it as a secret handshake and password exchange, ensuring both parties are who they claim to be and agreeing on a secure language for their conversation.
During this handshake, your browser and the bank’s server negotiate the specific cryptographic algorithms they will use for the session, including the encryption cipher, hashing function, and key exchange method. The bank’s server presents its digital certificate, which your browser then verifies with a trusted Certificate Authority (CA). If everything checks out, a unique symmetric session key is generated and securely exchanged, forming the secure tunnel. This entire process happens in milliseconds, utterly transparent to the user, yet profoundly crucial for your financial security.
Symmetric vs. Asymmetric Encryption
The world of online banking relies on a clever combination of two primary types of encryption: asymmetric and symmetric. Asymmetric encryption, also known as public-key cryptography, uses a pair of mathematically linked keys: a public key and a private key. The public key can be freely shared and is used to encrypt data, while the private key, kept secret by its owner, is the only key that can decrypt data encrypted with its corresponding public key. This system is foundational for securely exchanging the initial session key and verifying identities.
Once the initial secure channel is established using asymmetric encryption, the heavy lifting of actual data transfer is handled by symmetric encryption. With symmetric encryption, the same single key is used for both encrypting and decrypting data. This method is significantly faster and more efficient for large volumes of data, making it ideal for the continuous flow of transaction details and personal information during an online banking session. The secure exchange of this shared symmetric key, facilitated by the slower but more secure asymmetric methods, is a brilliant engineering compromise.
Digital Certificates and Trust
At the heart of verifying identity in online banking is the digital certificate. Issued by trusted third parties known as Certificate Authorities (CAs), these certificates act like digital passports for websites. When your bank’s server presents its certificate, it contains crucial information: the bank’s public key, its domain name, the CA’s digital signature, and an expiration date. Your browser automatically checks this signature against its own list of trusted CAs, ensuring the certificate is legitimate and hasn’t been tampered with.
This chain of trust is absolutely vital. If your browser can’t verify the certificate, it will issue a warning, indicating a potential security risk – a warning you should never ignore. A valid digital certificate assures you that you are indeed communicating with your bank and not an imposter trying to intercept your data. Without this robust system, the entire edifice of secure online communication would crumble, leaving us vulnerable to widespread phishing and man-in-the-middle attacks, even in 2026.
Hashing for Data Integrity
Beyond encryption, another unsung hero in securing online banking is cryptographic hashing. While encryption protects data confidentiality, hashing ensures data integrity – meaning the data hasn’t been altered during transit. A hash function takes an input (your transaction data, for example) and produces a fixed-size string of characters, known as a hash value or digest. Even a tiny change to the original data will result in a completely different hash value, making any tampering immediately obvious.
Before your encrypted data is sent, a hash is generated and often transmitted alongside it, typically signed by the sender. Upon receipt, the recipient generates a new hash of the decrypted data and compares it to the original hash. If they match, the data is confirmed to be intact and unaltered. This one-way, irreversible process is crucial because it provides an unforgeable fingerprint for every piece of information, adding another critical layer of security to online banking systems.
Beyond the Browser: End-to-End Security
While the browser-to-server connection is paramount, how encryption works in online banking systems extends far beyond that initial secure tunnel. Banks employ a multi-layered, “defense-in-depth” strategy. This includes encrypting data at rest within their databases, often using techniques like tokenization where sensitive payment information is replaced with a non-sensitive equivalent. This means that even if a database were breached, the stolen data would be largely useless without the corresponding decryption keys or tokenization mapping.
Furthermore, internal bank networks are heavily segmented and protected with strong encryption, firewalls, and intrusion detection systems. Multi-factor authentication (MFA) adds another formidable barrier, requiring more than just a password to access accounts. From the moment you initiate a transaction to its final processing and storage, your financial data is encased in multiple layers of cryptographic protection, ensuring its confidentiality and integrity throughout its lifecycle. It’s a comprehensive approach that recognizes every potential vulnerability.
The Ongoing Battle: Staying Ahead of Threats
The landscape of cyber threats is constantly evolving, and so too must encryption. Cryptographers and security experts are in a perpetual arms race, developing stronger algorithms to counter emerging threats, including the theoretical future threat of quantum computing. We’ve seen protocols evolve from SSL 3.0 to TLS 1.0, 1.1, 1.2, and now TLS 1.3, each iteration bringing enhanced security and efficiency. Banks invest massively in staying ahead, regularly updating their systems and adhering to the latest cryptographic standards.
For financial institutions, future-proofing their systems is not an option; it’s an imperative. They are actively researching and preparing for post-quantum cryptography, ensuring that even in 2026 and beyond, your financial transactions remain impervious to the most advanced attacks. While the technology is sophisticated, our role as users is equally important: staying vigilant against phishing, using strong, unique passwords, and enabling MFA are critical personal contributions to this collective security effort. It’s a shared responsibility.
Key Takeaways
- The TLS handshake is the critical first step, establishing a secure, encrypted communication channel between your browser and the bank.
- Online banking utilizes both asymmetric encryption for secure key exchange and symmetric encryption for efficient, high-volume data transfer.
- Digital certificates, issued by Certificate Authorities, are essential for verifying the identity of your bank’s website and preventing impersonation.
- Beyond the browser, banks employ layered security, including data at rest encryption, hashing for integrity, and multi-factor authentication, to ensure comprehensive protection.
Frequently Asked Questions
What is the primary protocol for encryption in online banking?
The primary protocol used for encryption in online banking today is Transport Layer Security (TLS), which is the successor to the older Secure Sockets Layer (SSL). When you see “https://” in your browser’s address bar, it signifies that TLS is actively encrypting the communication between your device and the bank’s server.
Can my encrypted banking data still be intercepted?
While the data packets themselves can technically be intercepted by malicious actors, the encryption makes them virtually unreadable without the correct decryption key. Modern cryptographic algorithms are incredibly robust; breaking them without the key would require computational power far beyond anything currently available, making interception without decryption practically useless.
How do I know if my banking session is encrypted?
You can easily verify if your banking session is encrypted by looking for “https://” at the beginning of the website address in your browser’s URL bar. Additionally, a padlock icon should appear, usually to the left of the URL. Clicking on this padlock often provides details about the digital certificate, confirming the site’s identity and the encryption in use.
Will encryption methods change significantly by 2026?
Encryption methods are continuously evolving. While the core principles of TLS and public-key infrastructure will likely remain, we can expect ongoing refinements, stronger algorithms, and potentially the introduction of quantum-resistant cryptography as a proactive measure against future threats. The security landscape of 2026 will undoubtedly feature even more robust and adaptive encryption techniques.
Conclusion
The intricate dance of encryption in online banking systems is a testament to human ingenuity in safeguarding sensitive information. It’s a complex, multi-layered defense system that operates silently in the background, providing the fundamental trust we now place in digital financial transactions. As a passionate expert in this field, I find it truly remarkable how these technologies empower us. Understanding this process demystifies our digital world and reinforces why we can confidently manage our finances online, knowing that our data is protected by an ever-evolving, formidable cryptographic shield.
Related Blogs
Published on May 06, 2026
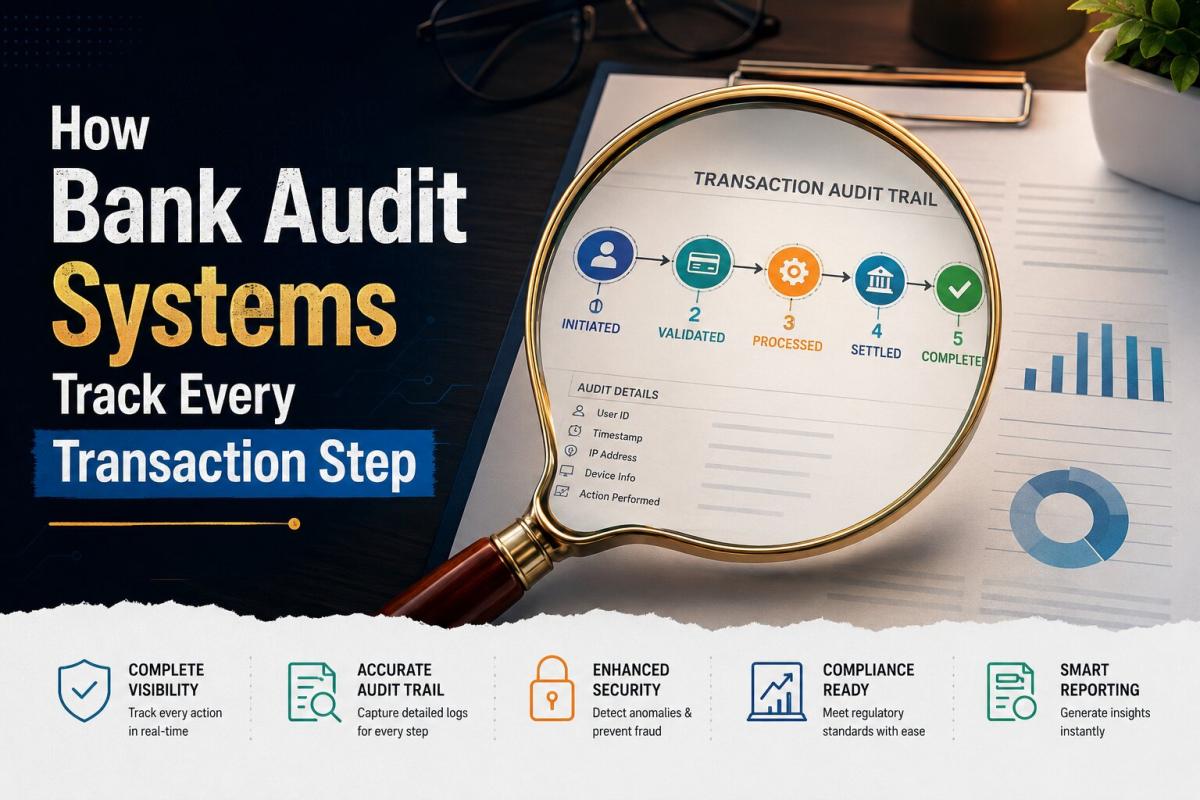
How Bank Audit Systems Track Every Transaction Step
Discover how bank audit systems track every transaction step using audit trails, real-time logging, and AI monitoring to ensure transparency, fraud detection, and regulatory compliance.
Priya Nair
Senior Compliance Editor at IFSC.co
Published on May 06, 2026
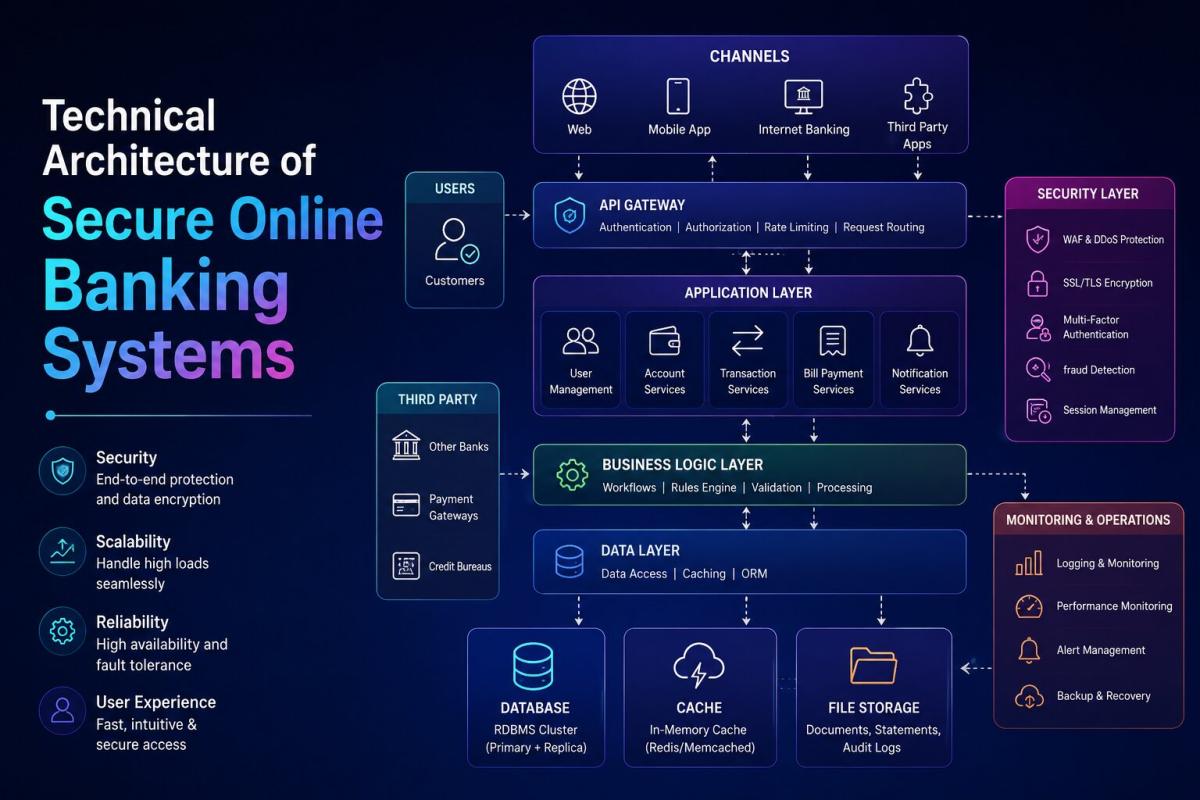
Technical Architecture of Secure Online Banking Systems
Explore the technical architecture of secure online banking systems, including layered security, encryption, authentication, APIs, and fraud detection that protect digital transactions.
Priya Nair
Senior Compliance Editor at IFSC.co
Published on Apr 28, 2026
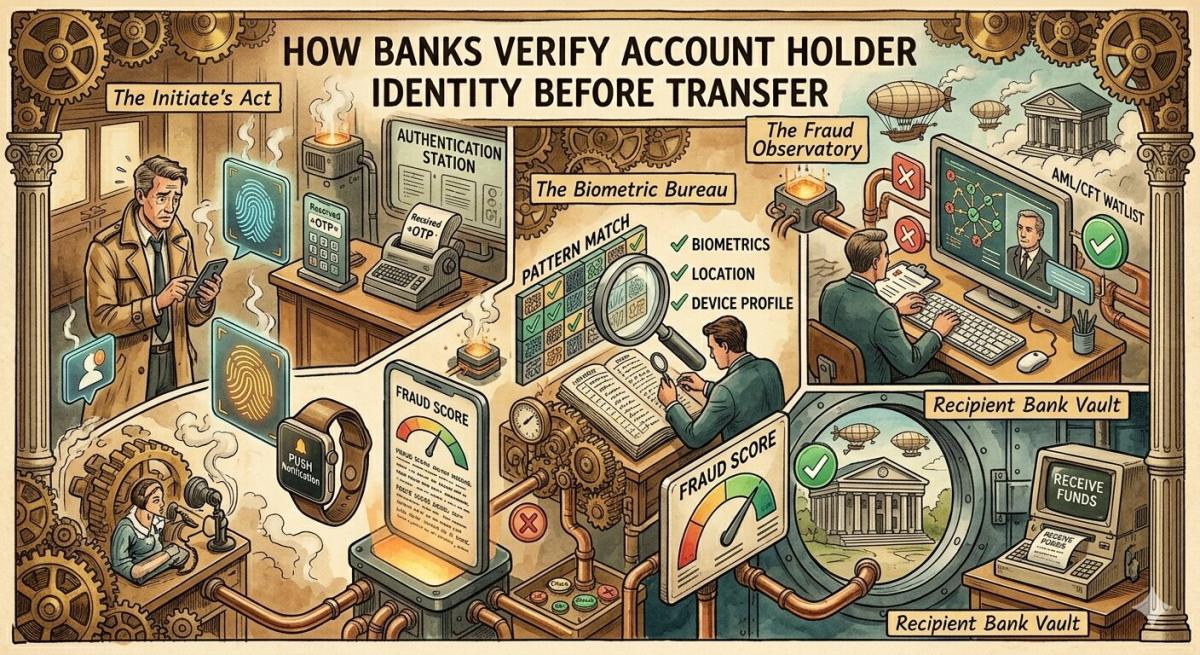
How Banks Verify Account Holder Identity Before Transfer
Learn how banks verify account holder identity before transfers using KYC, OTP, biometrics, and real-time fraud detection to ensure secure and compliant digital transactions.
Priya Nair
Senior Compliance Editor at IFSC.co

Published on Apr 28, 2026
What Causes Silent Bank Transaction Failures Without Alert
Discover the key causes of silent bank transaction failures, including network timeouts, API issues, system delays, and how banks resolve these hidden payment errors.
Priya Nair
Senior Compliance Editor at IFSC.co

Published on Apr 28, 2026
Real Time Bank Transaction Authentication Process Explained
Understand how real-time bank transaction authentication works using OTP, biometrics, encryption, and AI-driven fraud detection to secure digital payments instantly.
Priya Nair
Senior Compliance Editor at IFSC.co
calculate Financial Calculators
EMI Calculator
FD Calculator
GST Calculator
Lumpsum Calculator
Mutual Fund Returns Calculator
PPF Calculator
RD Calculator
SIP Calculator
SWP Calculator
article Latest Blog Posts
ELSS vs PPF vs NPS: Which Tax-Saving Investment Gives the Best Returns?
Compare ELSS vs PPF vs NPS to find the best tax-saving investment. Understand returns, lock-in periods, and features to choose what suits your goals.
SIP & Investing • 11 MINS READ
How to Start SIP with ₹500 Per Month: Beginner's Guide to Mutual Funds
Learn how to start a SIP with ₹500 per month in mutual funds. Simple beginner’s guide to investing, building wealth, and growing money with small steps.
SIP & Investing • 13 MINS READ
Senior Citizen FD Rates 2026: Which Banks Offer the Highest Interest?
Compare senior citizen FD rates in 2026 and find which banks offer the highest interest. Learn about returns, tenures, and tips to choose the best FD.
FD, PPF & Savings • 12 MINS READ
Sukanya Samriddhi Yojana (SSY): Interest Rate, Rules & Calculator Guide 2026
Learn about Sukanya Samriddhi Yojana (SSY) including eligibility criteria, required documentation, step by step application process, tax benefits explanation and comparison b/w SSY, PPF and FD
FD, PPF & Savings • 11 MINS READ
2 reasons why online banking is important in today’s COVID-19 situation
Discover why online banking became essential during COVID-19. Learn how digital banking ensured safety, convenience, and uninterrupted financial services.
Digital Banking • 4 MINS READ